Recent Articles
- Prime Secured
- April 29, 2024
The popularity of legacy WAN systems is waning for a number of reasons. Businesses are sending more and more traffic...
- Prime Secured
- April 22, 2024
An unfortunate truth about computer technology is that most equipment has a limited lifespan. Whether equipment breaks...
- Prime Secured
- April 16, 2024
Cyber, cyber, cyber—it seems that's all anyone talks about these days, and unfortunately for good reason. We...
- Prime Secured
- March 29, 2024
Most companies have some sort of disaster recovery plan in place, but many plans don’t survive an actual disaster. Data...
- Prime Secured
- March 13, 2024
In late February, an international law enforcement group known as the NCA (National Crime Agency) banded together to...
- Prime Secured
- March 1, 2024
Schools, stores, hospitals, churches, and similar organizations that operate across multiple locations often face...
- Prime Secured
- February 16, 2024
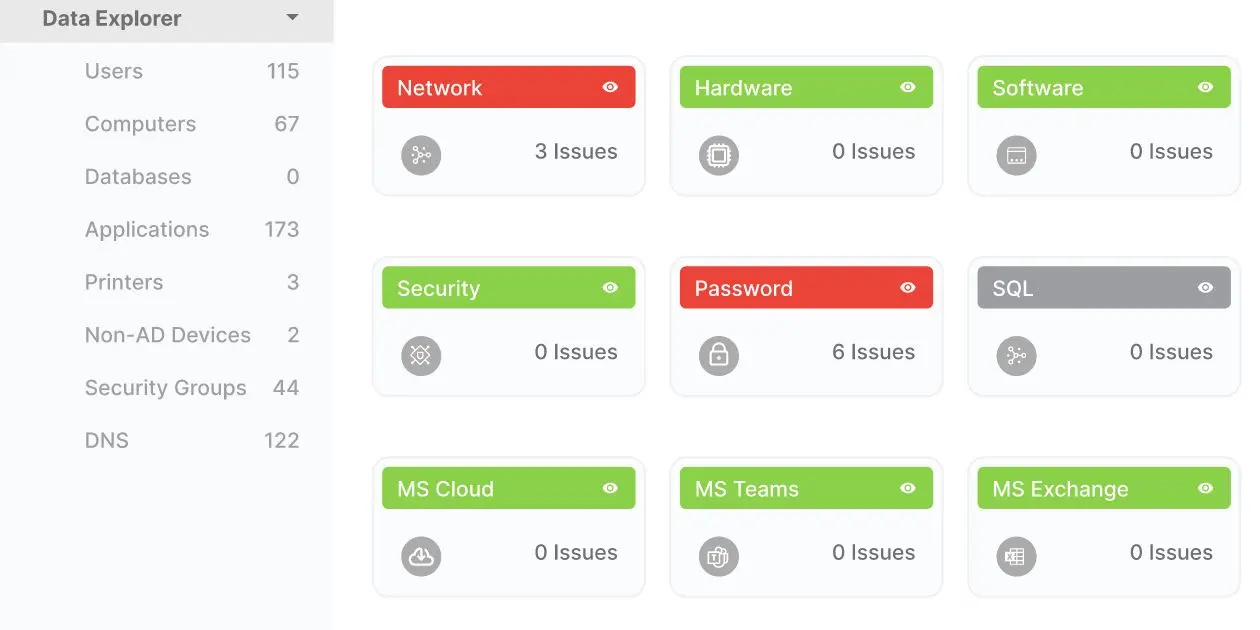
Do you know the current state of your IT environment? Maybe you were the one to choose your networking hardware and...
- Prime Secured
- January 31, 2024
A staggering 80% of security breaches are traced back to compromised passwords—that are either stolen, reused, or weak....
- Prime Secured
- January 19, 2024
Security isn’t convenient by nature—and, if it seems convenient and easy, the truth is that it really may not be...
- Prime Secured
- January 11, 2024
Cybersecurity Insurance a tool worth having Cybersecurity insurance is becoming an essential tool in our digital...
- Prime Secured
- December 29, 2023
Microsoft the Ultimate Business Suite. Isn't it remarkable how Microsoft's suite of business tools has become a staple...
- Prime Secured
- December 28, 2023
As we step into 2024 and reflect on the previous year, it's astonishing to witness the tremendous changes in...
- Prime Secured
- December 14, 2023
Identify Your Technology Roadblocks Are you feeling stuck due to your technology? You're not alone. It can be...
- Prime Secured
- December 4, 2023
Ready to get down to business budgeting? Ah, budget season, a time when numbers and spreadsheets dominate your...
- Prime Secured
- November 16, 2023
Are you getting the best value from your IT provider? Today, we're addressing a topic that might seem daunting for...
- Prime Secured
- November 2, 2023
Do you find budgeting for IT challenging? If so, you aren’t alone. Navigating the IT budgeting process can be a...
- Prime Secured
- October 25, 2023
Leverage E-Rate funds for better technology. With many of today's teaching materials going digital, technology has...
- Prime Secured
- October 24, 2023
The world of social media sharing & cybersecurity. Our lives have become intricately interwoven with social media. It...
- Prime Secured
- October 12, 2023
Managed IT it's the answer to your tech headaches. As a company grows, so do its IT needs—sometimes at an overwhelming...
- Prime Secured
- October 5, 2023
AI Cybersecurity Threats Are Advancing Join us on a journey back to the winter of 2022, a time when AI was just...
- Prime Secured
- September 26, 2023
Why Invest in Cybersecurity Training? You'veprobably heard about data breaches and cyberattacks happening all too...
- Prime Secured
- September 7, 2023
Prepare Your Remote Workforce for Battle Against Cybercriminals The working world, as we have come to know it, has...
- Prime Secured
- August 22, 2023
Protect from Within: How to Prioritize Employee Cybersecurity Training Over the past decade, organizations have found...
- Prime Secured
- June 30, 2023
In today's interconnected world, the rise of cybercrime poses a significant threat to individuals, businesses, and even...
- Prime Secured
- May 30, 2023
Artificial intelligence (AI) has brought about incredible advancements, but it has also empowered malicious actors to...
- Prime Secured
- May 1, 2023
Upgrade Your Cybersecurity with a Zero Trust Implementation Plan Have you heard of Zero Trust IT security? It's a...
- Prime Secured
- May 1, 2023
What is Zero Trust Security? Zero Trust security is a security model that assumes all devices, users, and applications...
- Prime Secured
- April 24, 2023
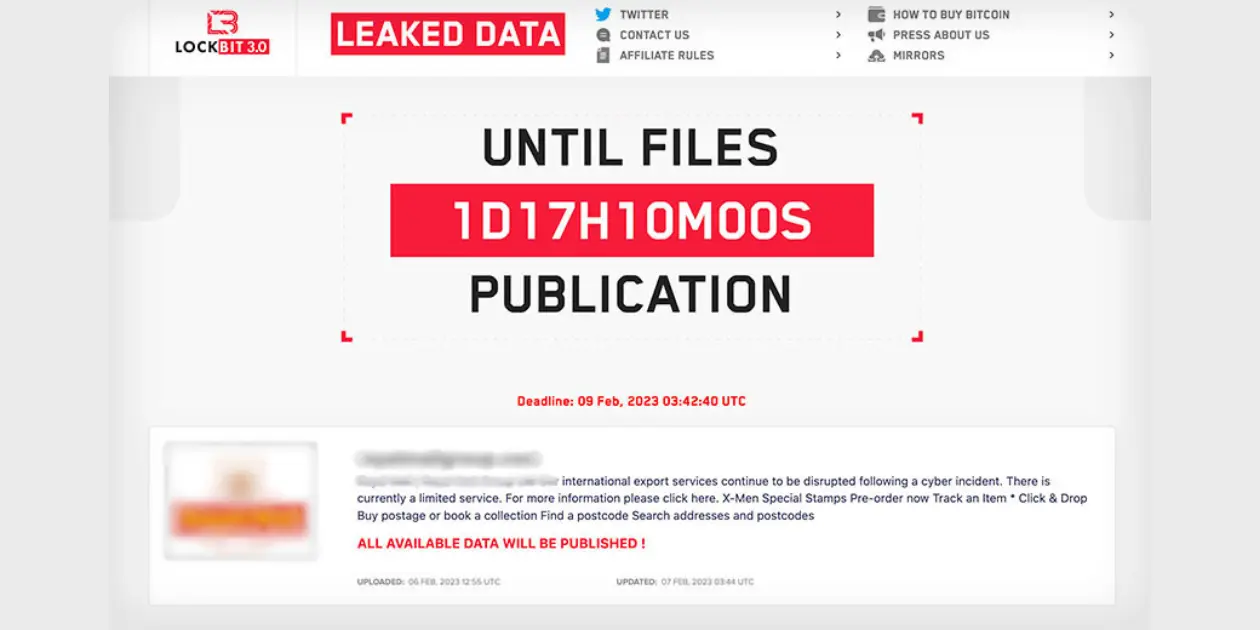
To Stop Ransomware, Let's Understand What It is Ransomware is a malicious software that encrypts files on a device or...
- Prime Secured
- April 5, 2023
Understand these Myths to Prevent Ransomware Are you worried about ransomware attacks? You're not alone. With the...
- Prime Secured
- March 23, 2023
Ask Yourself- Are You Happy? Switching IT providers can be a tough decision, especially if you have a long-standing...
- Prime Secured
- February 14, 2023
Not all IT service providers are created equal. When looking for an IT service provider to outsource your tech support,...
- Prime Secured
- February 2, 2023
As we move into 2023 and look back at the past few years, it’s almost hard to believe how much has changed in the...
- Prime Secured
- January 30, 2023
4 Practical Steps to Take When Hardware and Software Expire
- Prime Secured
- October 10, 2022
Data breaches have been on the rise due to the emergence of new cyber security threats. Cyber attack trends show that...
- Prime Secured
- September 6, 2022
Strengthen your Cybersecurity with Defense in Depth The current threat landscape is rapidly advancing, with...
- Prime Secured
- August 9, 2022
In today's evolving landscape, organizations are increasingly embracing the power of network as a service (NaaS) and...
- Prime Secured
- June 21, 2022
Nothing is more crucial to a business than stability. Yes, profit matters, but companies can achieve consistent profits...
- Prime Secured
- June 6, 2022
Can you name every program your organization uses to operate your enterprise?